
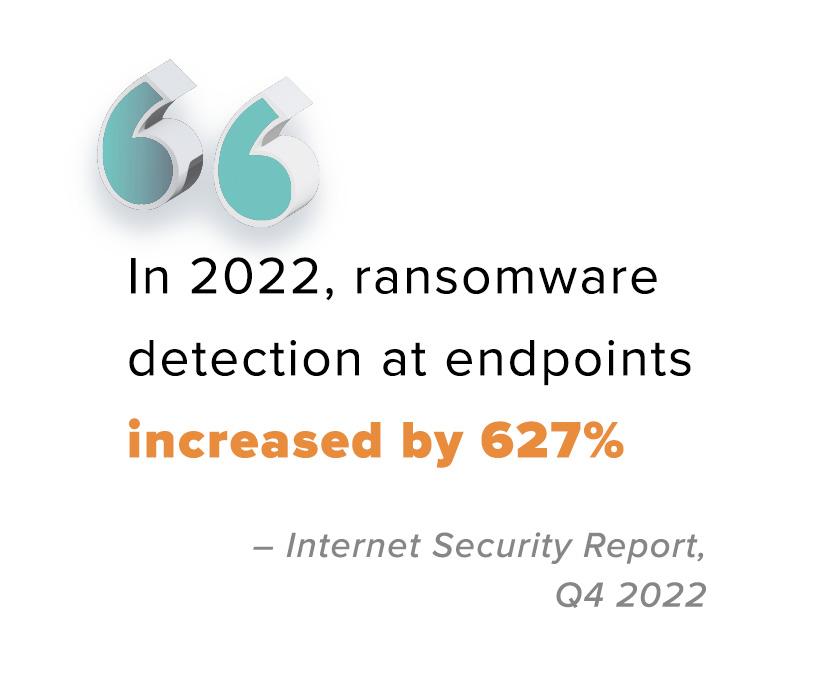
Despite concerted efforts from both public and private sectors, the ransomware attacks continues to escalate. Previously, cybercriminals hesitated to target healthcare and educational systems, but today, no industry or business size is exempt from the risk of ransomware. The global digital ecosystem is plagued by relentless and increasingly sophisticated ransomware threats.
Victim organizations feel the effects of ransomware long after the initial attack and can ruin consumer confidence in their brand. Victims suffer from data encryption, double extortion, exposure of data on the dark web or public sites, restoration challenges, and significant downtime. Executives are accountable for implementing risk management strategies to minimize vulnerabilities and safeguard their bottom line.
What is Endpoint Management?
Endpoint Management (EPM) refers to a comprehensive IT security solution for risk detection, application deployment, and patching. Hardware assets (such as desktops, laptops, and servers) are centrally controlled and actively managed to minimize risk. EPM can be deployed as an on-premises, hybrid cloud-based, or public cloud-based solution. When you leverage the expertise of an IT Solutions Provider with managed service proficiency, you can directly benefit from end-to-end management coverage that includes remote patching, application deployment, operating system monitoring, imaging, firmware updates, risk management, troubleshooting, security, and remediation.
Endpoint Management presents a centrally managed, hybrid cloud-based solution that leverages on-premises resources, cloud-driven automation, reporting, compliance automation, and deployment automation to minimize the attack surface of your network and perimeter.
The Importance of Endpoint Management
Endpoint Management provides full visibility into the status of applications, data points, and connections. EMP collects valuable data that assists executives in analyzing and evaluating performance metrics while executing corporate policies across the company network. EPM acts as a digital tether, limiting business exposure and improving asset management.
With the right tools and management system in place, EPM can enhance operational efficiencies, boost productivity among remote workforces, minimize outages, and maintain robust security measures.
Addressing Security Concerns
Open endpoints present easy targets for hackers. As organizations expand their digital footprint, security policies that were previously confined to office environments must be extended to remote workforces and personal devices. If a threat actor manages to infiltrate a single remote laptop, they can gain unauthorized access to an organization's network, files, and sensitive data - crippling the entire business.
In-house IT resources often lack the capacity to protect every endpoint against security threats using the tools at their disposal. Many companies struggle to track, update, and secure all devices connected to their business networks. Consequently, they require a solution that streamlines the security and management of multiple operating systems, data sources, assets, and enables seamless integration and proper configuration of security tools.
 |
Organizations must protect application functionality while minimizing their exposure to security risks. Solution Providers can seamlessly integrate customers' existing CCM (Configuration and Change Management) investments with new tools, transforming their environment into a reliable, scalable, and secure platform to boost productivity and visibility.
Increasing Visibility
Endpoint management solutions play a pivotal role in enhancing visibility and simplifying asset management. Deep visibility into your IT environment enables real-time threat detection, reduces response time, and informs business decisions. Endpoint management systems excel at promptly identifying and addressing issues, ensuring threats are mitigated quickly.
The ability to secure a wide range of devices and operating systems strikes a balance between management and access, with a primary focus on security and productivity. Enhanced digital scrutiny contributes to an improved employee experience and reduces the risk of infiltration.
Building Resilience
Corporate-owned devices are typically deployed to a distributed workforce, but personal devices must be centrally managed and secured as well. Each device must adhere to corporate-approved policies, software updates, and security measures through automated, cloud-based processes to ensure the safety of data and IT infrastructure. A Solutions Provider will deploy patch management, remote imaging, and application updates to ensure that endpoint resiliency and network security is enforced by robust management practices across the entire business.
By utilizing a centralized endpoint management platform, organizations can identify and eliminate redundant tool functionalities to streamline their operations and optimize resource allocation. Security measures are embedded into the endpoint management strategy and leverages automation to achieve scalability and efficiency.
Reporting and role-based controls play a crucial part in endpoint management, enabling users to effectively manage access to internal systems based on their user profile and responsibilities using the concept of least privilege. This helps to enforce security protocols and minimize the risk of unauthorized access.
Solution Providers collaborate closely with organizations to align an endpoint management solution with their unique security, technology, and operational needs. By integrating data availability, vulnerability monitoring, backup processes, and business continuity, these solutions provide a holistic approach to managing endpoints and ensuring the smooth operation of the business.
Implementing endpoint management solutions addresses several critical challenges, including the management of unpatched endpoints, mitigating security risks, facilitating remote accessibility, enabling seamless deployment of applications, and providing the capability to remotely shut down rogue or compromised accounts. EPM solutions have a direct impact on business outcomes when organizations realize the benefits of partnering with a Solution Provider to gain their comprehensive tool sets, attention to business security, and strategies that enhance their cybersecurity posture, streamline operations, and mitigate risks associated with endpoint vulnerabilities.
TBC as your Endpoint Management Provider
TBC is an IT Solutions Provider headquartered in Scottsdale, Arizona with 26 years of experience in cybersecurity and managed services. We work closely with our clients to identify security gaps, configure existing toolsets to effectively secure perimeters, and provide 24/7/365 monitoring services of IT environments.
TBC recently released a consolidated endpoint management product called Extended Threat Detection and Response (xTDR). TBC’s security engineers will not only manage digital security across your distributed workforce by securing remote endpoints and personal devices connected to your network, but they will actively hunt for threats to your environment. Our centralized endpoint management solution will give you the confidence to develop forward-thinking strategies to help secure your valuable data and limit the risk of cyberattacks.
.png)


