As more companies refuse to pay ransoms (only 41% of ransom demands were paid in 2022), cybercriminals are modifying their tactics from shutting down entire organizations with ransomware to using data exfiltration techniques to intimidate victims. Don't take this to mean that ransomware is dead – rather, you will need to implement yet another layer of cyber defense.
Because the attackers are not encrypting data, they can more easily remain in a network, moving laterally to stay undetected for longer. The result is that they can expand their reach to cause more significant harm and maximize profits. They can reach more victims willing to pay to stop their data and intellectual property from being published.
Data Exfiltration and Ransomware
Security and Risk Management leaders are prepared to combat disruptive ransomware with the people, processes, and technologies of cybersecurity solutions and business continuity plans. IT teams are well-versed in incident detection and response.
Data exfiltration is the ability to copy and export data without compromising the operability of an organization. Ransomware aims to paralyze company operations by encrypting data and then extorting payment in return for data recovery.
But data exfiltration often escapes detection because some can mimic legitimate software and traffic patterns as they move silently within the network. Once in the network, attackers can disable detection software and infect data backups. That’s why it is critical to build operational resiliency into your business and plan for the worst – with immutable backups, micro-segmentation, Extended Threat Detection and Response (xTDR), and a solid business continuity plan.
Often, the criminals have a complete picture of the victim – and can contact them directly, threaten them with public shame, and/or exposure of personal information like medical records, financial data, social security numbers, addresses, etc. Not only can threat actors inflict damage to the organization, but they can also target individual customers of impacted organizations.
The Victims
In California, the medical office of a Beverly Hills plastic surgeon experienced an attack and subsequent data exfiltration. The hackers not only sought payment from the medical office and posted sensitive information and photos of patients on a public site but also emailed patients and threatened to expose their photos and personal information if they did not pay individually.
Ransomware as a Service (RaaS) has made ransomware available to low-skilled criminals, broadening the attack landscape. Years ago, victims could "trust" particular ransomware gangs because they held a 'code among thieves,' but those days are gone. Encryption keys may not work – data can be destroyed. Then, data is available on the dark web even after ransom payments are made.
Cybercriminals continue to attack victims with double extortion or re-extortion and deny them peace or resolution. Double extortion is when the criminal exfiltrates data and encrypts it – so they can use it for sale or publication - or threaten to - while awaiting payment. Re-extortion is when cybercriminals continue to demand money, even after the ransom payment is made. In either case, there are no guarantees that your data will be recoverable, clean, or unpublished if you pay a ransom.
Many victims have successfully filed class action lawsuits against attacked organizations, claiming they did not do enough to protect their customers' data privacy. Organizations like Progress Software, Colonial Pipeline, Blackbaud, the City of Oakland, and Yum Brands, which have large cybersecurity budgets, have been sued because of ransomware attacks. Even the organizations that paid ransoms have found that their reputations and brand recognition suffered long-term damage despite taking action.
How to Protect your Data
How do cybercriminals get into your network in the first place? Often, employees' invite' them in by falling for phishing attacks. Or an exploited third-party vendor or software will unknowingly contaminate your network and spread the malware through your systems.
The CL0P ransomware gang has exploited widely used file-transfer services like MOVEit and GoAnywhere MFT to infiltrate their clients' networks and capitalize on threats to release sensitive personal or organizational data publicly. Ransomware and data exfiltration are more than expensive nuisances; they can undercut governments, financial institutions, and media enterprises, disrupt supply chains, and wreak havoc on individuals.
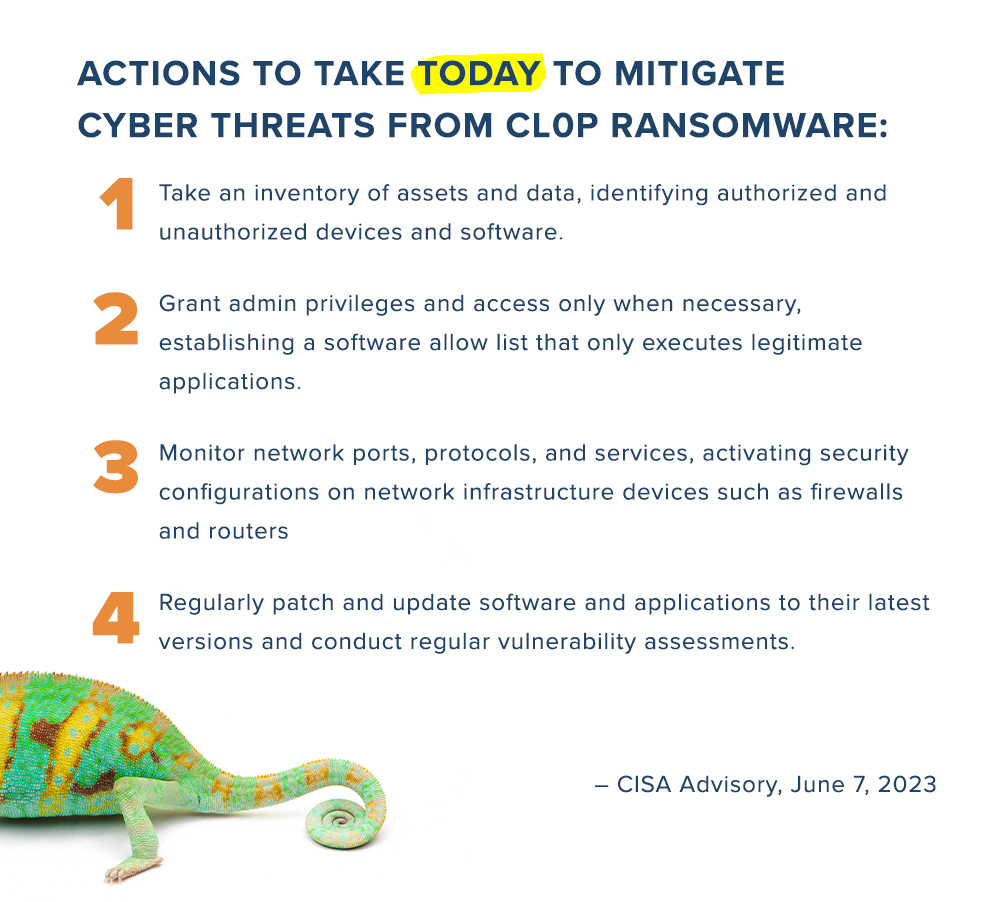
CISA recently released a basic but powerful advisory for IT teams to reduce the threat of data exfiltration and ransomware.
Cybersecurity and data protection solutions are constantly evolving to meet and defeat the endless tactics deployed by cybercriminals. You can’t relax your guard, but you can unburden your organization by investing in a partnership with an experienced Solutions Provider that can deliver comprehensive security, strong identity and access management, and data protection services.
Partner with TBC for Cybersecurity and Immutable Data Backups
TBC is an IT Solutions Provider based in Scottsdale, Arizona, with over 27 years of experience as a Managed Security Services Provider (MSSP) and Managed Services Provider (MSP). We offer comprehensive cybersecurity solutions managed by experienced, certified security architects and engineers using industry best practices and hand-picked tools and software to ensure positive business outcomes for our clients.
Our Data Backup and Disaster Recovery teams are constantly upskilling to ensure your data is protected, available, compliant, and restorable. If your IT teams need guidance from seasoned professionals, TBC offers individualized attention and prioritization in filling critical gaps and vulnerabilities to keep your business running.
TBC’s SOC provides constant vigilance over your systems, infrastructure, and network to ensure maximum productivity and reliability. We offer customized IT services and solutions to fit your current needs, and we will work with your leadership teams to roadmap solutions for your growth and profitability.
.png)